Managing NTFS permissions is a critical part of securing access to an organization’s confidential files and folders. IT admins often struggle to decide which permissions to grant to who, and, in most cases, employees have access to more data than they need. In organizations with large IT environments, admins deal with thousands of folders, unique permissions, security groups, group memberships, and more.

NTFS Permissions Management
In these complex environments, admins are more likely to experience trouble locating and fixing loopholes in assigned NTFS permissions; to address this, there are a few things admins can avoid that will go a long way in NTFS permissions management.
1) Assigning users direct access to folders.
The most common mistake admins make while assigning permissions is granting access permissions directly to a user. This can be a maintenance nightmare for admins if this user is deleted or changes their role, leaving admins to hunt for and remove orphaned SIDs and ACLs.
The best practice would be to create the right security group and assign the user to this group. Upon leaving the organization or changing roles, the user can simply be removed from the group and reassigned to another group according to the new role.
2) Granting Everyone or Authenticated Users groups full control of folders.
Another error admins make is granting full control to the Everyone group or the Authenticated Users group. subfolders enables unauthorized users to change NTFS permissions on files or folders. Admins must perform regular security audits of their file servers to find any instances where users have full control permissions and replace them with security group-based permissions.
3) Treating organizational units (OUs) like security groups.
Some admins treat OUs like permission groups when providing access to users; admins will grant OUs direct NTFS permissions to files and folders—most often to folders meant for a specific department’s use. This can be as problematic as providing users direct access to folders. In the event a staff member leaves the organization or is transferred, admins will be left scouring the network in search of orphaned SIDs to clean up in the ACLs.
4) Failing to identify broken NTFS permissions.
If an NTFS permission is broken, the inheritance of access control will not function correctly. This means that the permissions applied to a parent folder have not propagated down to the child folder, or the child folder has inherited permissions that are not applied to the parent folder.
Native NTFS permissions management tools don’t make it easy to identify these broken access-control lists (ACLs), making it a challenge for admins to locate and fix them, paving the way for maintenance issues in the future. What IT admins need is a comprehensive tool that can subfolder identify and fix broken NTFS permissions.
5) Setting NTFS permissions on a deep folder structure.
Organizations with no proper folder structure planning often have directories with multiple nested folders within. Assigning NTFS permissions to these nested folders can cause many problems, such as not knowing which security ACLs exist at the subfolder level.
Admins can prevent hidden permissions by ensuring the folder structure has limited levels of sub folders on which setting NTFS permissions is possible. Admins also need to keep tabs on the permissions each layer of the sub folder is inheriting. Although there are provisions to deny permissions at the folder level explicitly, it is better to have a minimalistic hierarchy for permissions management.
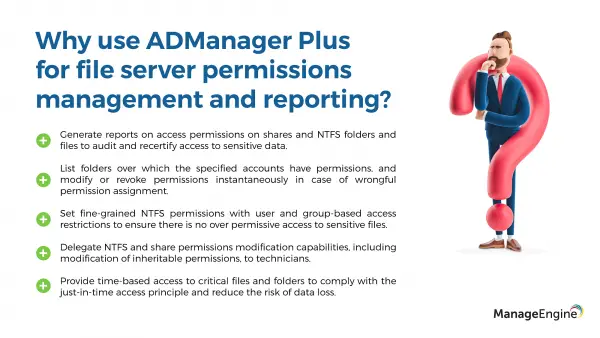
The main issue faced by AD admins is the lack of a transparent tool that can easily spot and resolve these issues without requiring any complex PowerShell scripts. ADManager Plus has been consistently voted to be one among the top tools for NTFS permissions reporting and management.
Get started with a free trial, and make NTFS permissions management and reporting easy!